The Acronyms Blog
Acronyms News
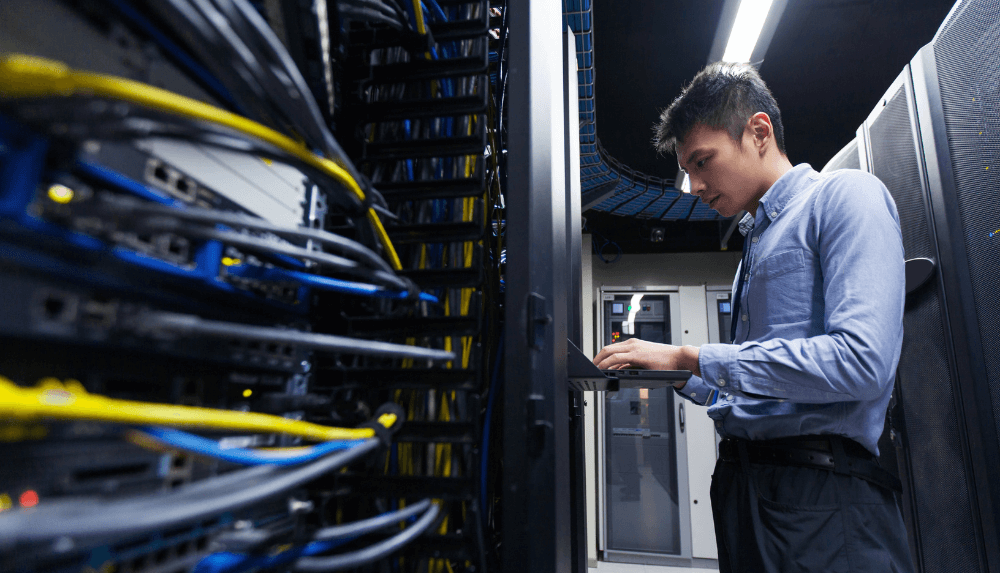
IT Infrastructure
Click to view an archive of our IT Infrastructure blog posts.
Internet Connectivity
Click to view an archive of our Internet Connectivity blog posts.
VoIP Telephony
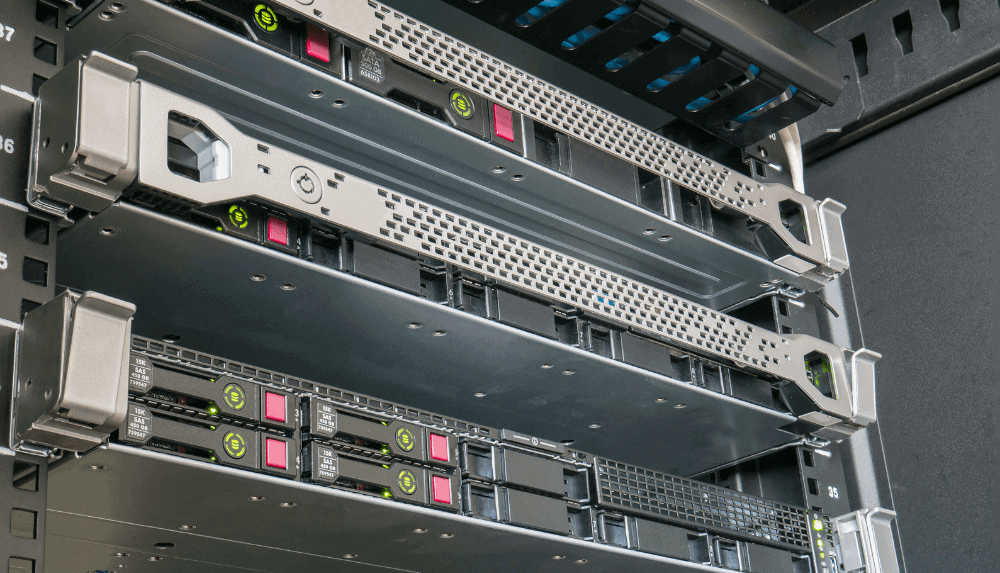
Disaster Recovery
Click to view an archive of our Disaster Recovery blog posts.
Book a no-obligation consultation today.
We provide free consultations to all businesses that may wish to utilise our services. This allows us to better understand your business, your aims and any challenges you may face, before making recommendations.